Archives
- By thread 5279
-
By date
- June 2021 10
- July 2021 6
- August 2021 20
- September 2021 21
- October 2021 48
- November 2021 40
- December 2021 23
- January 2022 46
- February 2022 80
- March 2022 109
- April 2022 100
- May 2022 97
- June 2022 105
- July 2022 82
- August 2022 95
- September 2022 103
- October 2022 117
- November 2022 115
- December 2022 102
- January 2023 88
- February 2023 90
- March 2023 116
- April 2023 97
- May 2023 159
- June 2023 145
- July 2023 120
- August 2023 90
- September 2023 102
- October 2023 106
- November 2023 100
- December 2023 74
- January 2024 75
- February 2024 75
- March 2024 78
- April 2024 74
- May 2024 108
- June 2024 98
- July 2024 116
- August 2024 134
- September 2024 130
- October 2024 141
- November 2024 171
- December 2024 115
- January 2025 216
- February 2025 140
- March 2025 220
- April 2025 233
- May 2025 239
- June 2025 303
- July 2025 91
-
Digital innovation for retailers and CPG companies
Re:think
How retail and CPG can lead with tech
by "McKinsey Quarterly" <publishing@email.mckinsey.com> - 02:07 - 4 Jun 2025 -
Learn to build flow-based UIs – workshop with our CTO
Hi,
Recently you were interested in workflowbuilder.io. Next week, our CTO, Łukasz Jaźwa, is running a live workshop on how to build flow-based user interfaces using Workflow Builder SDK and React — as part of the upcoming React Summit.
Where & When?
- June 9th, 4–7 PM CET
- Remote, via Zoom
It’s a session full of real-world techniques, shortcuts, and expert code insights. As a bonus, you’ll also open-source access to Workflow Builder (non-commercial license).
Would you like me to send over the details?
Best,
 --
--
Ruslana Brykaliuk
Sales Development Representative
by "Ruslana Brykaliuk" <ruslana.brykaliuk@workflowbuilder.io> - 07:49 - 4 Jun 2025 -
Re: Business update..?
Hi,
I am still waiting for your reply,
Please let me know if you are interested in my services below.
Thanks,
From: Sartaj Khan
Sent: 02 May 2025 22:30
Subject: Just reply
Hi There,
Greetings of the day!
Would you be interested in building an app for your business? We have catered several clients needs in the below domains:-
Travel Apps
Real estate Apps
Restaurant Apps
E-Commerce Apps (both single vendor and multiple vendors)
GPS/Taxi/Food Delivery Apps
Website Development
If you are interested in any of our app services, let us know your project requirements or perhaps name an existing app that you think is similar to your requirement. We will suggest an action plan for you to consider after reviewing your needs.
Thanks,Sarta
by "Sartaj Khan" <sartaj.khan33@hotmail.com> - 04:14 - 4 Jun 2025 -
Wholesale Aquarium Pumps from China | Durable & 24H Battery Life
Dear Info,
Are you sourcing cost-effective aquarium pumps with long battery life for your wholesale business? JINGYE Electric Co., Ltd offers:
Battery-powered air pumps (24H+ runtime)
Mini submersible pumps (3W-10W, 110-240V)
Silent internal filters (under 25dB)
With 15 years of expertise, we supply pet industry distributors in India, Russia, and Southeast Asia, ensuring stable quality and MOQ 5 PCS flexibility.
Attached catalog highlights:
2024 Best-selling models
Bulk order discounts (5%-15% off)
OEM packaging support
Visit www.jingyeaquarium.com or reply to request samples. Let’s discuss how to boost your margins!
Sincerely,
YAN
WhatsApp:008615819960484
by "Caisy Furxer" <caisyfurxer@gmail.com> - 01:45 - 4 Jun 2025 -
What will it take to achieve metabolic health for all?
On McKinsey Perspectives
A $5.65 trillion opportunity 




Brought to you by Alex Panas, global leader of industries, & Axel Karlsson, global leader of functional practices and growth platforms
Welcome to the latest edition of Only McKinsey Perspectives. We hope you find our insights useful. Let us know what you think at Alex_Panas@McKinsey.com and Axel_Karlsson@McKinsey.com.
—Alex and Axel
•
A major health concern. Obesity has become a major public health issue that affects nearly 900 million adults globally. The condition has significant health and economic consequences, McKinsey Senior Partners Drew Ungerman and Hemant Ahlawat and their coauthors explain. Obesity heightens the risk of many other diseases, including type 2 diabetes, dementia, and depression. It also has adverse effects on labor force participation and productivity: According to McKinsey Health Institute estimates, obesity will be linked to $2.76 trillion in lost GDP each year in 2050.
—Edited by Belinda Yu, editor, Atlanta
This email contains information about McKinsey's research, insights, services, or events. By opening our emails or clicking on links, you agree to our use of cookies and web tracking technology. For more information on how we use and protect your information, please review our privacy policy.
You received this email because you subscribed to the Only McKinsey Perspectives newsletter, formerly known as Only McKinsey.
Copyright © 2025 | McKinsey & Company, 3 World Trade Center, 175 Greenwich Street, New York, NY 10007
by "Only McKinsey Perspectives" <publishing@email.mckinsey.com> - 01:42 - 4 Jun 2025 -
The part of AI most companies are missing
The part of AI most companies are missing
Hi MD Abul,
I was reading through the latest news over coffee this morning, something about Amazon deploying 750,000 robots and planning to save $16 billion a year with AI by 2032.
And for some reason, it didn’t just strike me as “big tech news.”
It felt familiar. Like déjà vu.
Because we’ve seen this play before.
And we’ve misread it before, too.Amazon’s warehouses are running like a well-oiled machine, robots sorting, drones delivering, and AI optimizing every move. It’s impressive, no doubt. But here’s the thing:
They didn’t just throw AI at a problem and hope it would fix things.
They redesigned their operations around it.
They rewired the way they work, end to end.And that’s the part most companies miss.
We see it all the time, organizations investing in new tools, automation, cloud platforms, AI… but the core of how they operate? It stays the same. Same structure. Same workflows. Same mindset.
That’s why we’re talking more and more about Digital Enterprise Operations (DEO) at Third Stage.
It’s not about adding tech to a broken process, it’s about rethinking the way your business runs in a digital world.If you’re exploring AI, automation, or a system overhaul, the question isn’t “What tool should we buy?”
It’s “What kind of business are we trying to become?”
That’s the shift.
And if you’re ready to make it, we’ll be diving deep into these exact conversations at our Digital Stratosphere conference this August-strategy, systems, AI, and how to build something that actually works.
Our theme this year is Mission: AI-Possible.
Join us in Denver!Use the code "earlybird" for 20% off your ticket(s)!
Best regards,
Eric Kimberling
Third Stage Consulting 384 Inverness Pkwy Suite Suite #200 Englewood Colorado 80112 United States
You received this email because you are subscribed to Marketing Information from Third Stage Consulting.
Update your email preferences to choose the types of emails you receive.
Unsubscribe from all future emails
by "Eric Kimberling" <eric.kimberling@thirdstage-consulting.com> - 09:49 - 3 Jun 2025 -
Learn from the funnel building Phenom! (free training)
Thursday she’s breaking down how she does it.We’re just 2 days away!
Russell and Kathryn are training YOU on how to get certified and tap into the MASSIVE BACKLOG of people asking, “Do you know anyone that can build my funnel??”
And just so you know… Russell invited funnel-building phenom, Kathryn Jones Lish, to co-host it with him.
Let me just say this about Kathryn:
✅ She’s a best-selling author.
✅ She’s a Two Comma Club Award winner.
✅ She’s built a 7-figure business selling funnels.
✅ She’s helped thousands of people just like you do the same.
But this is the REAL STORY:
She doesn’t just know how to build funnels… She knows how to launch and scale a funnel building business!
And that’s the reason this training will be massively valuable!!
If you have any interest in turning funnel building funnel building into a legit & profitable business (Or lucrative side-hustle)...
Get your seat reserved today!
REGISTER FOR THE FREE SALES FUNNEL BUILDER TRAINING HERE >>
Who: Russell Brunson and Kathryn Jones Lish
When: Thursday, June 5 @ 10AM PT / 1 PM ET
Where: LIVE on Zoom (not pre-recorded)
Why: Because the opportunity is real, and we want to show you how to claim it!
See you in two days!
© Etison LLC
By reading this, you agree to all of the following: You understand this to be an expression of opinions and not professional advice. You are solely responsible for the use of any content and hold Etison LLC and all members and affiliates harmless in any event or claim.
If you purchase anything through a link in this email, you should assume that we have an affiliate relationship with the company providing the product or service that you purchase, and that we will be paid in some way. We recommend that you do your own independent research before purchasing anything.
Copyright © 2018+ Etison LLC. All Rights Reserved.
To make sure you keep getting these emails, please add us to your address book or whitelist us. If you don't want to receive any other emails, click on the unsubscribe link below.
Etison LLC
3443 W Bavaria St
Eagle, ID 83616
United States
by "Todd Dickerson (ClickFunnels)" <noreply@clickfunnelsnotifications.com> - 07:06 - 3 Jun 2025 -
Re: Cost?
Hi,
Good morning!
I noticed a few areas on your website that could be improved. I’d be happy to share a detailed analysis with you, outlining specific changes that could help enhance your online presence.
Would you be open to receiving a customized report along with a brief recommendation?
Thank you
by "Lusia Zeb" <lusia80018@hotmail.com> - 02:02 - 3 Jun 2025 -
How Netflix Runs on Java?
How Netflix Runs on Java?
Netflix is a masterclass in backend engineering at scale. Behind the seamless playback, tailored recommendations, and cross-device consistency lies an intricate architecture powered by Java.͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ ͏ Forwarded this email? Subscribe here for moreKubernetes Quick-Start Guide (Sponsored)
Cut through the noise with this engineer-friendly guide to Kubernetes observability. Get a fast-track reference to essential kubectl commands and critical metrics — from disk I/O and network latency to real-time cluster events. Perfect for scaling, debugging, and tuning your workloads without sifting through endless docs.
Disclaimer: The details in this post have been derived from the articles/videos shared online by the Netflix Engineering Team. All credit for the technical details goes to the Netflix Engineering Team. The links to the original articles and videos are present in the references section at the end of the post. We’ve attempted to analyze the details and provide our input about them. If you find any inaccuracies or omissions, please leave a comment, and we will do our best to fix them.
Netflix is a masterclass in backend engineering at scale. Behind the seamless playback, tailored recommendations, and cross-device consistency lies an intricate architecture powered by Java.
The majority of Netflix’s backend services run on Java. This might surprise engineers who’ve watched the rise of Kotlin, Go, Rust, and reactive frameworks. But Netflix isn’t sticking with Java out of inertia. Java has matured, and so has the ecosystem around it. Modern JVMs offer powerful garbage collectors. Spring Boot has become both extensible and reliable. And with the arrival of virtual threads and structured concurrency, Java is reclaiming its place in high-throughput, low-latency system design, without the overhead of reactive complexity.
In this article, we’ll walk through how Netflix uses Java today. We will also cover the following topics:
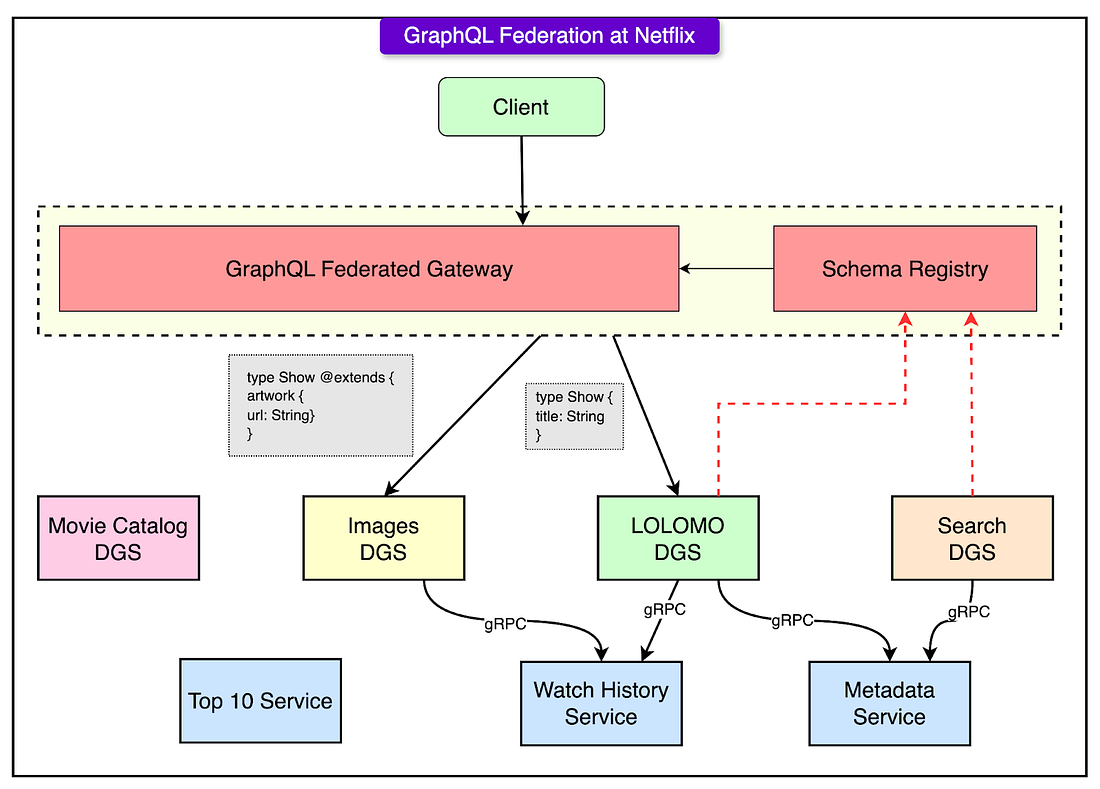
The architectural backbone of Netflix: a federated GraphQL platform connecting client apps to dozens of Java backend services.
The concurrency model: how Java virtual threads and modern garbage collectors change performance and reliability.
The evolution: a company-wide migration off technical debt and onto Spring Boot, JDK 21+, and beyond.
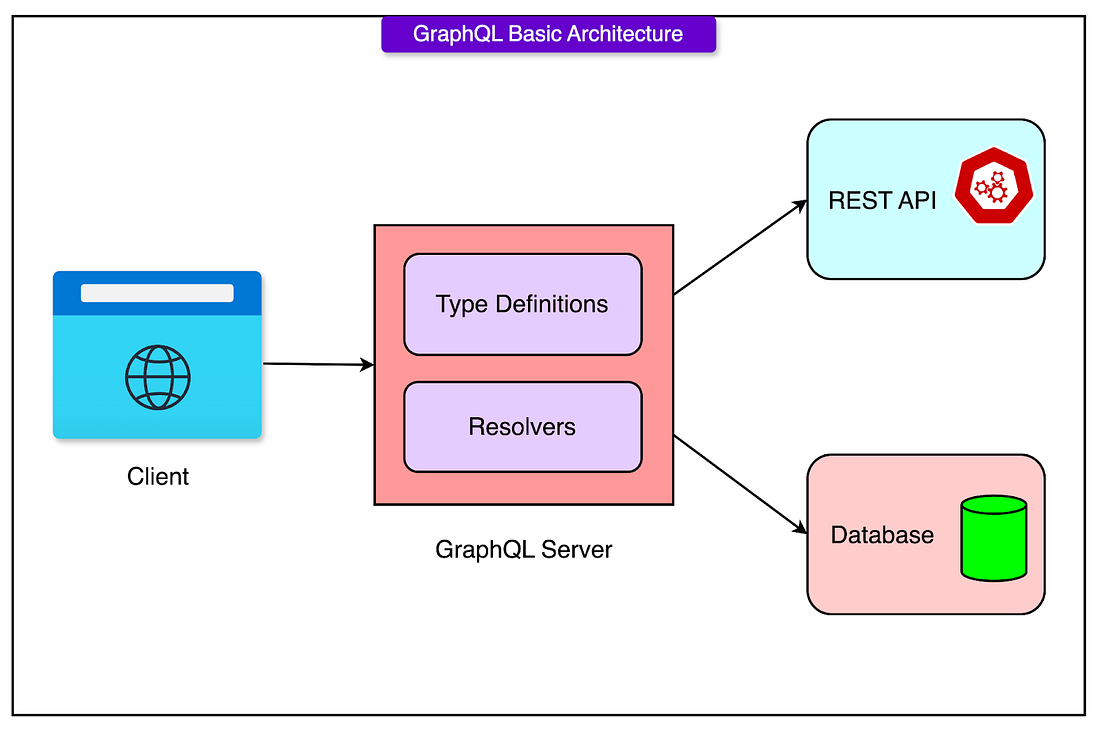
Backend Architecture with the GraphQL Foundation
At the heart of Netflix’s backend lies a federated GraphQL architecture. This is the primary abstraction through which all client applications interact with backend data. The model provides both flexibility and insulation: clients can express exactly what they need, and backend teams can evolve their services independently.
Every GraphQL query from a Netflix client, whether from a smart TV, phone, or browser, lands at a centralized API Gateway. This gateway parses the query, decomposes it into subqueries, and routes those to the appropriate backend services.
Each backend team owns a Domain Graph Service (DGS), which implements a slice of the overall GraphQL schema. Every Domain Graph Service (DGS) at Netflix is a Spring Boot application.
The DGS framework itself is built as an extension of Spring Boot. This means that it supports the following features:
Dependency injection, configuration, and lifecycle management are handled by Spring Boot.
GraphQL resolvers are just annotated Spring components.
Observability, security, retry logic, and service mesh integration are implemented using Spring’s mechanisms.
Netflix picked Spring Boot because it’s proven at scale and a long-lived technology at Netflix. It’s also extensible as Netflix layers in their modules for security, metrics, service discovery, and more.
The DGSs register their schema fragments to a shared registry. The gateway then knows which service is responsible for which field. This turns one “monolithic” schema into a fully federated, independently deployable graph.
This separation of schema ownership enables:
Independent deployability of services
Schema-driven collaboration between frontend and backend
Cleaner boundaries between domains (for example, recommendations vs. user profiles)
The key idea is that backend services own their part of the graph, not just their internal data.
Build Your Own Production-Ready Agent
Few outside major AI labs have optimized LLM agents with reinforcement learning. But Will Brown and Kyle Corbitt have.
In this first-of-its-kind course, they’re teaching engineers how to:
Choose the right agent pattern for your use case
Integrate MCP tools with Notion, Linear, and Slack
Evaluate where and why agents fail
Understand reinforcement learning without the math
3 weeks, 2x/week lectures with live coding/prompting, office hours, and Discord. Requires familiarity with Python and high-level AI/ML concepts.
Starts June 16th. Use code BYTEBYTEGO to save $100.
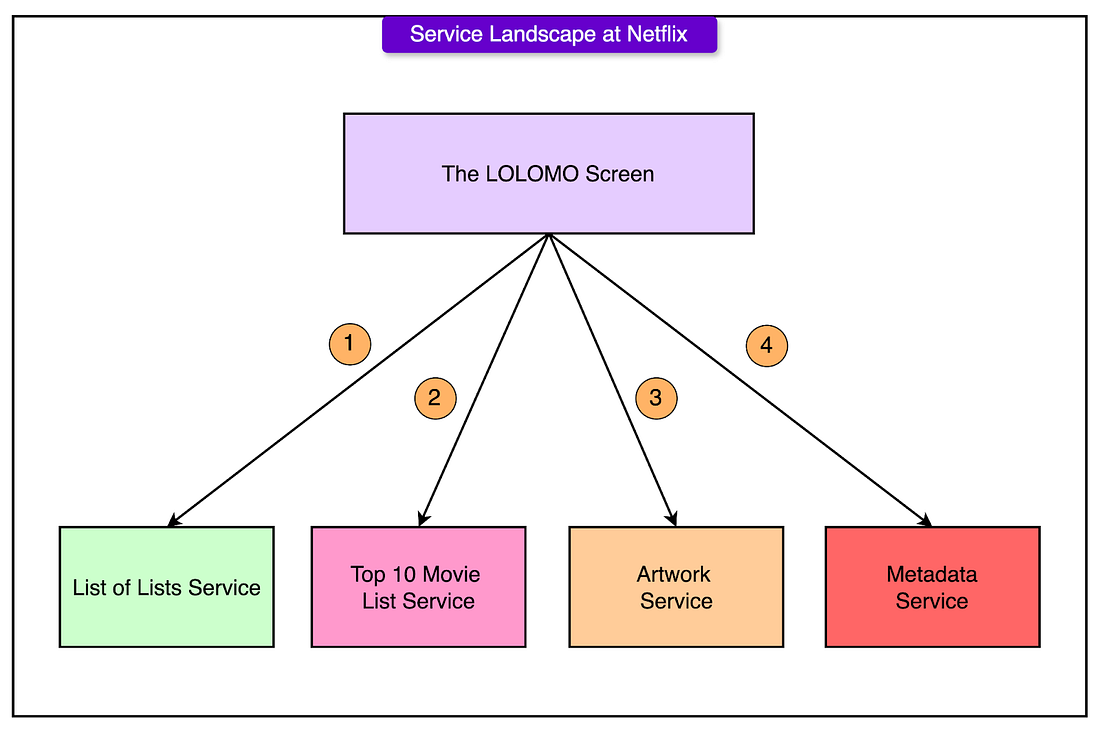
Microservice Fan-out: What a Query Hits
Behind the scenes, even a simple query, like fetching titles and images for five shows, fans out across multiple services:
The API Gateway receives the request.
It contacts 2–3 DGSs to resolve fields like metadata, artwork, and availability.
Each DGS may then fan out again to fetch from data stores or call other services.
This fan-out pattern is essential for flexibility but introduces real complexity. The system needs aggressive timeouts, retry logic, and fallback strategies to prevent one slow service from cascading into user-visible latency.
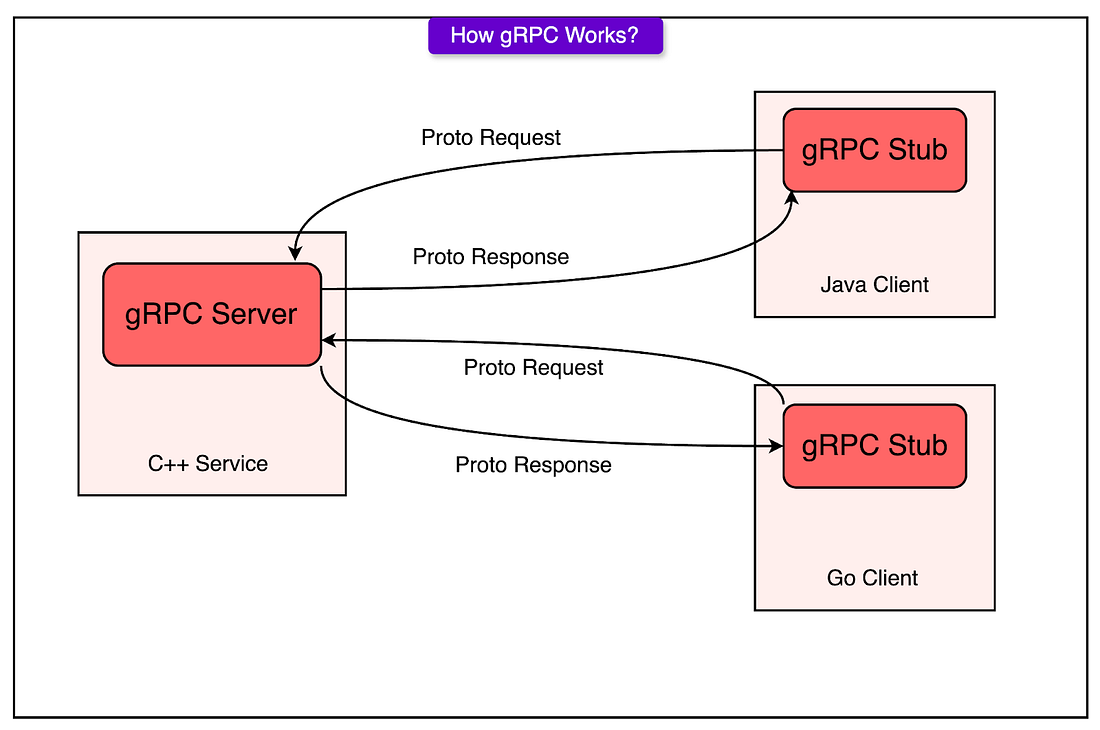
Protocol Choices
Between the client and the gateway, Netflix sticks with HTTP and GraphQL over standard web protocols. This ensures compatibility across browsers, mobile apps, and smart TVs.
Inside the backend, services communicate over gRPC: a high-performance, binary protocol that supports efficient service-to-service calls. gRPC enables:
Low-latency communication
Strong typing via Protocol Buffers
Easy interface evolution
This separation makes sense: GraphQL is great for flexible, client-driven data fetching, while gRPC excels in internal RPC-style interactions.
JVM Evolution
Until recently, much of Netflix’s Java codebase was stuck on JDK 8. The problem wasn’t inertia but lock-in. A custom in-house application framework, built years earlier, had accumulated layers of unmaintained libraries and outdated APIs. These dependencies had tight couplings and compatibility issues that made upgrading anything beyond JDK 8 risky.
In this setup, service owners couldn’t move forward independently. Even when newer Java versions were technically available, the platform wasn’t ready. Teams had little incentive to upgrade because it required effort with no immediate benefit. The result was stalled progress across the board.
Breaking that cycle required a direct approach. Netflix patched the incompatible libraries themselves, not by rewriting everything, but by forking and minimally updating what was necessary to make it compatible with JDK-17. In practice, this wasn’t as daunting as it sounds. Ultimately, only a small number of critical libraries required intervention.
In parallel, the company began migrating all Java services (around 3000) to Spring Boot. This wasn’t a simple lift-and-shift. They built automated tooling to transform code, configure services, and standardize deployment. While the effort was significant, the result is a unified platform that can evolve in step with the broader Java ecosystem.
Now, the baseline across most teams is Spring Boot on JDK 17 or newer. A few legacy services remain for backward compatibility, but they were the exception.
Once services moved to JDK 17, the benefits became obvious:
The G1 garbage collector, already in use, showed a significant improvement: roughly 20% less CPU time spent on GC without changing application code.
Fewer and shorter stop-the-world pauses led to fewer cascading timeouts in distributed systems.
Higher overall throughput and better CPU utilization became possible, especially for high RPS services.
Generational ZGC
G1 garbage collector served Netflix well for years. It struck a balance between throughput and pause time, and most JVM-based services used it by default. But as traffic scaled and timeouts tightened, the cracks showed.
Under high concurrency, some services saw stop-the-world pauses lasting over a second, long enough to cause IPC timeouts and trigger retry logic across dependent services. These retries inflated traffic, introduced jitter, and obscured the root cause of failures. In clusters running at high CPU loads, G1's occasional latency spikes became an operational burden.
However, the introduction of generational ZGC changed the game.
ZGC had been available in prior Java versions, but it lacked a generational memory model. That limited its effectiveness for workloads where most allocations were short-lived, like Netflix’s streaming services.
In JDK 21, generational ZGC finally arrived. It brought a modern, low-pause garbage collector that also understood object lifetime. The effect was immediate:
Pause times dropped to near-zero, even under heavy load.
Services no longer timed out during GC pauses, which led to a visible reduction in error rates.
With fewer garbage collection stalls, fewer upstream requests failed, reducing cluster-wide pressure.
Clusters ran closer to CPU saturation without falling over. Headroom previously held in reserve for GC safety was now available for real workloads.
From an operator’s perspective, these improvements were significant. A one-line configuration change (switching from G1 to ZGC) translated into smoother behavior, fewer alerts, and more predictable scaling.
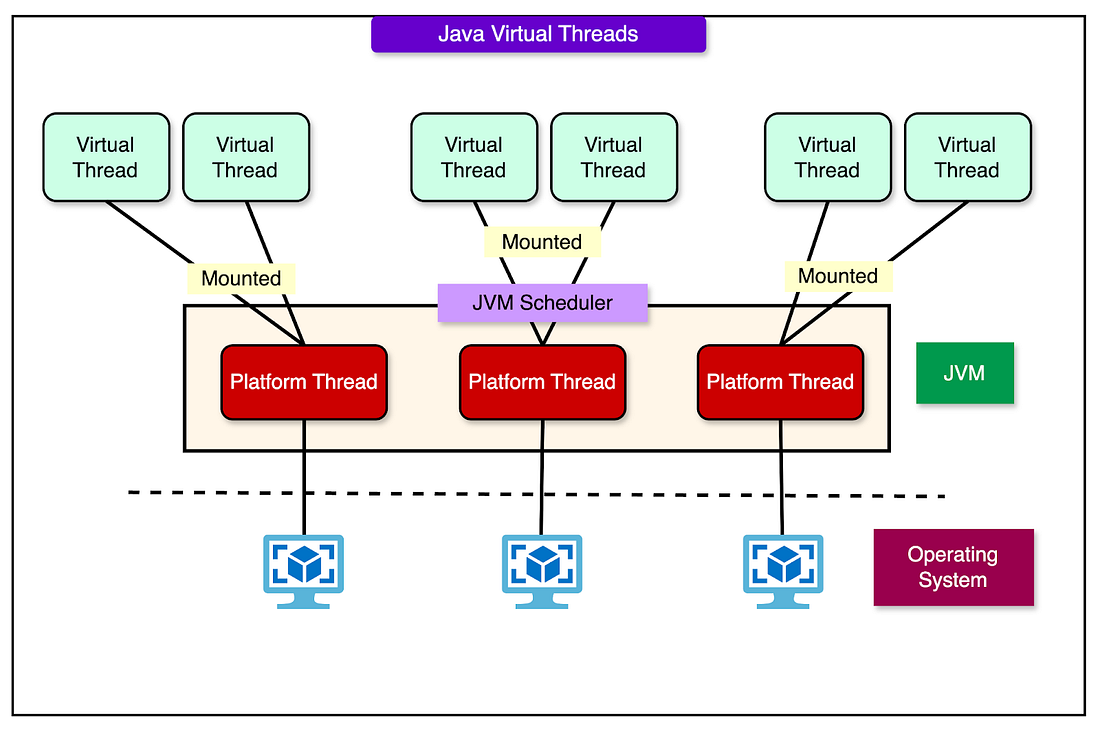
Use of Java Virtual Threads
In the traditional concurrency model, each request handler runs on a separate thread.
For high-throughput systems, this leads to high thread counts, inflated memory usage, and scheduling overhead. Netflix faced exactly this situation, particularly in its GraphQL stack, where individual field resolvers might perform blocking I/O.
Parallelizing these resolver calls manually was possible, but painful. Developers had to reason about thread pools, manage “CompletableFutures”, and deal with the complexity of mixing blocking and non-blocking models. Most didn’t bother unless performance made it unavoidable.
With Java 21+, Netflix began rolling out virtual threads. These lightweight threads, scheduled by the JVM instead of the OS, allowed blocking code to scale without monopolizing resources. For services built on the DGS framework and Spring Boot, the integration was automatic. Resolvers could now run in parallel by default.
See the diagram below that shows the concept of Java virtual threads.
Take the common example of a GraphQL query that returns five shows, each requiring artwork data. Previously, the resolver fetching artwork URLs ran serially, adding latency across multiple calls. With virtual threads, those calls now execute in parallel, cutting total response time significantly, without changing the application code.
Netflix wired virtual thread support directly into their frameworks:
Spring Boot–based services automatically benefit from parallel execution in field resolvers.
Developers don’t need to use new APIs or change annotations.
The thread scheduling model remains abstracted away, preserving familiar development workflows.
This opt-in-by-default model works because virtual threads impose almost no overhead. The JVM manages them efficiently, making them suitable even in high-volume paths where traditional thread-per-request models fall apart.
Trade-Offs
Virtual threads aren't magic. Early experiments revealed a specific failure mode: deadlocks caused by thread pinning.
Here's what happened:
Some libraries used synchronized blocks or methods.
When a virtual thread enters a synchronized block, it becomes pinned to a physical platform thread.
If many pinned virtual threads block while holding locks, and the pool of platform threads is exhausted, the system can deadlock. No threads can make progress, because the thread that holds the lock can’t be scheduled.
Netflix encountered this exact scenario in production.
The issue was serious enough that Netflix temporarily backed off aggressive virtual thread adoption. But with JDK 24, this problem was addressed directly: the JVM rewrote the internals of synchronized to avoid unnecessary thread pinning.
With that change in place, the engineering team was able to once again push forward. The performance and simplicity gains are too good to ignore, and now the risk has been meaningfully reduced.
Why Netflix Moved Away from RxJava?
Netflix helped pioneer reactive programming in the Java ecosystem. RX Java, one of the earliest and most influential reactive libraries, was born in-house. For years, reactive abstractions shaped the way services handled high-concurrency workloads.
Reactive programming excels when applied end-to-end: network IO, computation, and data storage all wrapped in non-blocking, event-driven flows. But that model requires total buy-in. In practice, most systems fall somewhere in between: some async libraries, some blocking IO, and a lot of legacy code. The result is a brittle mix of concurrency models that’s hard to reason about, hard to debug, and easy to get wrong.
One frequent pain point was combining a thread-per-request model with a reactive HTTP client like WebClient. Even when it worked, it introduced two concurrency layers (one blocking, one non-blocking), creating complex failure modes and resource contention. It was effective for certain fan-out use cases, but operationally expensive.
The introduction of virtual threads shifted the equation. As mentioned, they allowed thousands of concurrent blocking operations without the overhead of traditional threads. Combined with structured concurrency, developers can express complex async workflows using plain code, without the callback hell of reactive programming.
Having said that, reactive programming still has its place. In services with long IO chains, backpressure concerns, or streaming workloads, reactive APIs remain useful. However, for the bulk of Netflix’s backend, which involves RPC calls, in-memory joins, and tight response times, virtual threads and structured concurrency offer the same benefits with lower complexity.
The Spring Boot Netflix Stack
Netflix standardizes its backend services on Spring Boot, not as an off-the-shelf framework, but as a base for a deeply integrated, extensible platform. Every service runs on what the team calls “Spring Boot Netflix”: a curated stack of modules that layer company-specific infrastructure into the familiar Spring ecosystem.
This design keeps the programming model clean. Developers use standard Spring annotations and idioms. Under the hood, Netflix wires in custom logic for everything from authentication to service discovery.
The Spring Boot Netflix stack includes:
Security integration with Netflix’s authentication and authorization systems, exposed through standard Spring Security annotations like @Secured and @PreAuthorize.
Observability support using Spring’s Micrometer APIs, connected to internal tracing, metrics, and logging pipelines built to handle Netflix-scale telemetry.
Service mesh integration for all traffic via a proxy-based system (built on ProxyD), handling TLS, service discovery, and retry policies transparently.
gRPC framework based on annotation-driven programming models, letting engineers write gRPC services with the same approach as REST controllers.
Dynamic configuration with “fast properties”: runtime-changeable settings that avoid service restarts and enable live tuning during incidents.
Retryable clients wrapped around gRPC and WebClient to enforce timeouts, retries, and fallback strategies out of the box.
Netflix stays closely aligned with Spring Boot upstream. Minor versions roll out to the fleet within days. For major releases, the team builds tooling and compatibility layers to smooth the upgrade path.
The move to Spring Boot 3 required migrating from javax.* to jakarta.* namespaces. It was a breaking change that affected many libraries. Rather than wait for external updates, Netflix built a Gradle plugin that performs bytecode transforms at artifact resolution time. This plugin rewrites compiled classes to use the new Jakarta APIs, allowing Spring Boot 2-era libraries to work on Spring Boot 3 without source changes.
Conclusion
Netflix’s Java architecture in 2025 isn’t a relic of the past, but a deliberate, modern engineering system. What makes it interesting isn’t the choice of language, but the way that choice is continuously reevaluated, optimized, and aligned with real-world constraints.
The system isn’t static. Netflix pushed past the limits of Java 8 by aggressively upgrading its stack, not by rewriting it. It embraced Spring Boot as a foundation but extended it to meet the unique demands of a global streaming platform. It adopted GraphQL for flexibility, virtual threads for concurrency, and ZGC for performance.
Some key takeaways are as follows:
Java is still competitive when treated as an ecosystem. Netflix extracts significant performance gains from modern JVM features. It doesn’t settle for default settings or old frameworks. Evolution is deliberate.
Owning the platform enables speed. Building in-house tooling for patching, transforming, and deploying applications turns upgrades from risk into routine. Platform ownership is a leverage for them.
Virtual threads reduce complexity. They preserve a familiar coding style while scaling better under load. The payoff is cleaner code, fewer bugs, and simpler mental models.
Tuning infrastructure and not just code improves reliability. Upgrading the garbage collector and optimizing thread behavior led to fewer timeouts, lower error rates, and more consistent throughput across the board.
References:
SPONSOR US
Get your product in front of more than 1,000,000 tech professionals.
Our newsletter puts your products and services directly in front of an audience that matters - hundreds of thousands of engineering leaders and senior engineers - who have influence over significant tech decisions and big purchases.
Space Fills Up Fast - Reserve Today
Ad spots typically sell out about 4 weeks in advance. To ensure your ad reaches this influential audience, reserve your space now by emailing hi@bytebytego.com.
Like
Comment
Restack
© 2025 ByteByteGo
548 Market Street PMB 72296, San Francisco, CA 94104
Unsubscribe
by "ByteByteGo" <bytebytego@substack.com> - 11:38 - 3 Jun 2025 -
Subverting tradition: revolutionary design of carbide valve stem and sleeve
Hello Info,
Hope this email find your well.
We are a professional manufacturer of valve tungsten carbide wear parts.Such as:carbide cage,choke trim,seat ,stem,plug and sleeve etc.
Product range up tp 12 inches.Our factory good at making non-standard products according to the drawing.
Any question,Call me , let ' s talk more !

Your friend
Genevieve
Zhuzhou Chuangrui Cemented Carbide Co.,ltd
Xintangpo,Middle HongQi Road,Hetang District,Zhuzhou City,Hunan,China.
Email:lydia@zzcrcarbide.com
Mobile:+86 18173348105
Whatspp/wechat: 0086 18173348105
website : www.zzcrcarbide.com
by "Genevieve" <Genevieve@carbidecreator.com> - 11:38 - 3 Jun 2025 -
She’s a funnel building Phenom… This will be incredible!
Thursday she’s breaking down how she does it.We’re just 2 days away from one of the most exciting live trainings I’ve ever hosted…
And this time, I’m not doing it alone!
I’ve invited my good friend and absolute funnel-building phenom, Kathryn Jones Lish, to co-host it with me.
If you don’t know Kathryn yet… let me just say this:
✅ She’s a best-selling author.
✅ She’s a Two Comma Club Award winner.
✅ She’s built a 7-figure business selling funnels.
✅ She’s helped thousands of people just like you do the same.
But the real reason I asked her to join me is simple:
She doesn’t just know how to build funnels… She knows how to launch and scale a funnel building business!
And that’s the reason this training will blow your mind and be SOOOO valuable!!
If you have any interest in turning funnel building funnel building into a legit & profitable business (Or lucrative side-hustle)...
Then this training is your moment.
REGISTER FOR THE FREE SALES FUNNEL BUILDER TRAINING HERE >>
Who: Russell Brunson (Me!) and Kathryn Jones Lish (Funnel Builder Phenom!)
When: Thursday, June 5 @ 10AM MT / 1PM ET
Where: LIVE on Zoom (not pre-recorded)
Why: Because the opportunity is real, and we want to show you how to claim it!
See you in two days!
Russell Brunson
P.S. – Don’t forget, you’re just ONE funnel away…
© Prime Mover LLC
By reading this, you agree to all of the following: You understand this to be an expression of opinions and not professional advice. You are solely responsible for the use of any content and hold Prime Mover LLC and all members and affiliates harmless in any event or claim.
If you purchase anything through a link in this email, you should assume that we have an affiliate relationship with the company providing the product or service that you purchase, and that we will be paid in some way. We recommend that you do your own independent research before purchasing anything.
Copyright © 2025 Prime Mover LLC. All Rights Reserved.
To make sure you keep getting these emails, please add us to your address book or whitelist us. If you don't want to receive any other emails, click on the unsubscribe link below.
Prime Mover LLC
3443 W Bavaria St
Eagle, ID 83616
United States
by "Russell Brunson" <newsletter@marketingsecrets.com> - 11:34 - 3 Jun 2025 -
Save the date. Agentic AI awaits
New Relic
 June 2025
June 2025New Relic Now: 25 June at 10am BST Join us at New Relic Now to learn about our latest Agentic AI innovations. In this virtual event, you’ll:- Turn insights into actions—explore Intelligent Observability transforming data into proactive, actionable intelligence.
- Gain industry perspectives—hear from Service Now and other leaders on agentic AI's profound impact.
Level up your skills—build agentic proficiency and predictive capability with demos from our product team.
Register now 
Accedo: Unlocking the observability blueprint for video streaming success Watch this episode to learn how Accedo, in conversation with our Chief Customer Officer Arnie Lopez, leverages New Relic to proactively optimize user experiences, minimize disruptions, and keep viewers engaged and coming back for more.Watch now 

AWS Summits EMEA
At the upcoming AWS Summits in June, we'll be showcasing our latest innovations, hosting demos, and offering insights into how New Relic can empower your AWS cloud journey.- Stockholm, Wednesday 4th June
- Hamburg, Thursday 5th June
- Madrid, Wednesday 11th June
Connect with us and explore the future of observability and performance monitoring in the cloud!
NRU Observability Workshop Series On-demand
Catch up on our series of 90 minute online workshops designed to enhance your skills and get you ready for securing the New Relic Certification of your choice. Whether you’re a seasoned professional or just starting your observability journey, our courses are designed to propel your career forward with New Relic and observability.
IDC names New Relic an observability leader in Europe
Download the report to see how our customisable platform helps leading European organisations break down silos, streamline operations, and deliver exceptional digital experiences.
Read the reportHow Generative AI changes everything about the observability industry
Just as the internet and smartphones have become essential for modern business strategies, GenAI will soon become an integral part of every company's growth plan, and organisations will need to adapt and innovate to stay competitive in this new era of AI-driven technology, or risk being left behind.
Learn moreGuide to structured logging in Python
Add structure to your Python logs, making it easier to extract meaningful information from your telemetry data.
Learn more
Alerts not triggering as expected?
Alerts are only helpful if they’re received. If your alerts aren’t triggering, it might be a threshold error. We can help you troubleshoot.Not an existing New Relic user? Sign up for a free account to get started!

Need help? Let's get in touch.



This email is sent from an account used for sending messages only. Please do not reply to this email to contact us—we will not get your response.
This email was sent to info@learn.odoo.com Update your email preferences.
For information about our privacy practices, see our Privacy Policy.
Need to contact New Relic? You can chat or call us at +44 20 3859 9190.
Strand Bridge House, 138-142 Strand, London WC2R 1HH
© 2025 New Relic, Inc. All rights reserved. New Relic logo are trademarks of New Relic, Inc
by "New Relic" <emeamarketing@newrelic.com> - 05:02 - 3 Jun 2025 -
Excelling as a leader: Growth
Change your mindset Email 1 of 7
Are you a growth leader?
Welcome to “The McKinsey Publishing Guide to excelling as a leader.” In this first email, we’ll dive into the beliefs and behaviors shared by growth leaders. Driving sustainable growth requires the right mindset, strategy, and capabilities. Here are some steps that could help you foster success.
Growth leaders generate 80 percent more shareholder value than their peers over a ten-year period—but about a quarter of companies don’t grow at all. And between 2010 and 2019, only one in eight achieved more than 10 percent revenue growth annually.
“Growth leaders set, communicate, and commit to growth consistently and without significant resourcing,” write McKinsey’s Michael Birshan, Biljana Cvetanovski, Rebecca Doherty, Tjark Freundt, Greg Kelly, Erik Roth, Ishaan Seth, and Jill Zucker.
Check out these insights to learn how to make and follow through on a purposeful choice to grow.This email contains information about McKinsey’s research, insights, services, or events. By opening our emails or clicking on links, you agree to our use of cookies and web tracking technology. For more information on how we use and protect your information, please review our privacy policy.
You received this email because you subscribed to “The McKinsey Publishing Guide to excelling as a leader.”
Copyright © 2025 | McKinsey & Company, 3 World Trade Center, 175 Greenwich Street, New York, NY 10007
by "McKinsey Publishing Guides" <publishing@email.mckinsey.com> - 03:10 - 3 Jun 2025 -
Fast fashion: An industry in flux
On McKinsey Perspectives
6 ways to decarbonize 




Brought to you by Alex Panas, global leader of industries, & Axel Karlsson, global leader of functional practices and growth platforms
Welcome to the latest edition of Only McKinsey Perspectives. We hope you find our insights useful. Let us know what you think at Alex_Panas@McKinsey.com and Axel_Karlsson@McKinsey.com.
—Alex and Axel
•
Rising popularity. Compared with other retailers, fast fashion brands accelerate their production cycles so they can offer shoppers the chance to update their wardrobes frequently, even with limited budgets. In 2023, 40% of US consumers and 26% of UK consumers purchased from two major fast fashion brands, McKinsey Senior Partners Anita Balchandani and Gemma D’Auria and coauthors share in The State of Fashion 2025 report. These retailers have not just strengthened their position in the US; they are now the country’s primary online marketplaces for fashion.
•
Sustainability challenges. Most fashion brands are finding it difficult to stay on track with their 2030 decarbonization goals, with 40% actually increasing their emissions since making earlier sustainability commitments. But tackling emissions doesn’t have to be as expensive as fashion leaders may think. McKinsey research shows that most fashion companies can cut their emissions by more than 60% for less than 1 to 2% of their revenues. Explore our McKinsey Explainers entry “What is fast fashion?” for six ways fashion companies can accelerate decarbonization.
—Edited by Ramya DRozario, editor, Gurugram
This email contains information about McKinsey's research, insights, services, or events. By opening our emails or clicking on links, you agree to our use of cookies and web tracking technology. For more information on how we use and protect your information, please review our privacy policy.
You received this email because you subscribed to the Only McKinsey Perspectives newsletter, formerly known as Only McKinsey.
Copyright © 2025 | McKinsey & Company, 3 World Trade Center, 175 Greenwich Street, New York, NY 10007
by "Only McKinsey Perspectives" <publishing@email.mckinsey.com> - 01:48 - 3 Jun 2025 -
Exploring Collaboration Opportunities in Automotive Shock Absorbers
Dear Info,
Greetings from Henghong Intelligent Equipment Co.,Ltd!
We are professional in R&D,production and sales of automotive shock absorbers.Our team has explored your website and noticed significant synergies between our product lines.With in-depth knowledge of your market,we are eager to share valuable insights and explore potential collaborations with you.
Would you like to accept our catalogue?It could open up new avenues for common development.
Best Regards!
Echo Gao
by "Maricordoba Ugo" <maricordobaugo26@gmail.com> - 10:35 - 2 Jun 2025 -
Hello Dear Friend
Dear Friend,
Greetings to you and your family.
My name is Mr. Abdul Rahman, The current Auditor of a bank here in Ouagadougou, Burkina Faso, West Africa. I have a transaction of US$9.5Million dollars for transferring into your home bank account for our mutual benefits and I need your total and 100% cooperation and assistance to realize this task.
Further details about the fund, its source and who will stand as a business partner to consulting. enterprise so that my bank can transfer this fund into your receiving bank account immediately as I have your positive response. You must assure me that everything will be handled confidentially as I am assuring you that all your details required for this transaction are all safe and secure. We will never lack again in life if we can join hands together for making this deal a success.
It has been over 9 years now that in my department we discovered an abandoned sum of US$9.500.000 (Nine million Five hundred thousand US dollars) In an account belongs to consulting enterprise in our country Burkina Faso that political party sign a contract with him and move huge amount of Funds into their various overseas counterparts bank accounts through the help of their Political advisers.
Most of the funds which they transferred out of West Africa were realized from material consultants, these are the funds meant for the development of our country Burkina Faso and their various Nations being taken away for their greedy and selfish ambition.
Their Political advisers always inflated the amounts before transferring it into foreign accounts, so I also took the opportunity to divert part of these funds, hence I am aware that there is no official trace of how much was transferred as all the accounts used for such transactions were being closed after each transfer.
I as the major Account Officer to most of those politicians and the then Foreign Remittance Dept Director of the bank, when I discovered that they were using me to succeed in their greedy invents, I also cleaned some of their banking records from the Bank files and no one ever cared to ask me because the money was too much for them to control. They laundered over US$964 Million Dollars during the process.
As I am sending you this message, I have the ability to transfer the diverted Nine Million Five Hundred Thousand Dollars ($9.5 M) into your own bank account abrade from an escrow account belonging to no one in the bank.
The bank is anxious now to know who his business partner to the consulting enterprise is because they have made a lot of profits with the funds. It is more than Nine years now and most of the politicians are no longer using our bank to transfer funds overseas as most of them have died and the rest are no more in power.
The US$9.5 Million Dollars has been lying fallow and I don't want to retire from the bank without transferring the funds to a foreign account to enable me share the proceeds with the receiver. The money will be shared 60% for me and 40% for you with expenses. There is no one coming to ask you any question whatsoever about the funds because I secured everything. Further details shall be mailed to you if only you show any sign of seriousness and interest.
Best Regard,
Mr.Abdul Rahman
by "Abdulaiye Rahmani" <abdulaiyer67@gmail.com> - 08:52 - 2 Jun 2025 -
Solution of Mixing Plant and Sand&Gravel Crushing Equipment
Dear Info,
I hope this email finds you well.
This is Yiwa from Run Tian Zhi Ke Mechanical Equipment Co. Ltd. We are focused on the manufacturing of construction machine for more than 20 years. Posses over 100 self-developed patents. Our products are sold to Europe, Southeast Asia, Africa and other regions.
We supply stabilized soil plant, concrete mixing plant, asphalt mixing plant, crushing and screening plant,Construction waste processing production line.
Our customer complaint rate is zero. We always focus on customers’ needs.
Our products are mainly used for Construction of highways, railways, municipal engineering, hydro-power, ports, bridges, large constructions, main, etc..
And if possible, we are glade to invite you to coming to visit our intelligent factory.
Really look forward to hearing from you.
Your sincerely
Yiwa
Marketing Manager
Mobile/Whataspp#:(+86) 18890380993 | Email: market@runtian-global.com
Hunan Runtianzhike Machinery Manufacturing Co.,Ltd
Website: www.runtian-global.com
ADD:No.9, Shengyuan Road, Yueyang High-tech Industrial Park, Hunan, China
by "sales01" <sales01@rtzkhn.com> - 05:24 - 2 Jun 2025 -
[FREE TRAINING] Funnel Building Training
This could be the key to success in turbulent times.Are you a “trapped professional”?
Here’s what I mean: You’re slaving away at a job you hate… working for a boss you can’t stand… Desperately wanting to make a change… IF THAT’S YOU… ⬇️⬇️⬇️
I get it… the news can be a little overwhelming and scary…
But here’s my humble advice… When everyone else is getting scared and hunkering down…
That’s when successful entrepreneurs MAKE THEIR MOVES!
i.e. Successful people have the foresight to know… When everyone else zigs… YOU ZAG!!!
Becoming a funnel builder is a skill that puts you back in control of your financial future… NO MATTER what’s happening with the economy. (Because it’s in SUCH HIGH DEMAND!!)
If you’re stuck… If you’re a little nervous… If you want to regain your confidence and create a career that allows you to control your destiny… What have you got to lose by exploring this opportunity!
REGISTER FOR THE FREE SALES FUNNEL BUILDER TRAINING HERE >>
See you Thursday!
© Etison LLC
By reading this, you agree to all of the following: You understand this to be an expression of opinions and not professional advice. You are solely responsible for the use of any content and hold Etison LLC and all members and affiliates harmless in any event or claim.
If you purchase anything through a link in this email, you should assume that we have an affiliate relationship with the company providing the product or service that you purchase, and that we will be paid in some way. We recommend that you do your own independent research before purchasing anything.
Copyright © 2018+ Etison LLC. All Rights Reserved.
To make sure you keep getting these emails, please add us to your address book or whitelist us. If you don't want to receive any other emails, click on the unsubscribe link below.
Etison LLC
3443 W Bavaria St
Eagle, ID 83616
United States
by "Todd Dickerson (ClickFunnels)" <noreply@clickfunnelsnotifications.com> - 04:07 - 2 Jun 2025 -
Elevate Your Products with Xinfu’s 2’-FL – Safety, Expertise, Supply Strength
Dear Info ,
I’m Qihan Wang from Hangzhou Xinfu Science & Technology Co., Ltd. It’s a pleasure to connect with you.
At Xinfu, we specialize in developing high-value ingredients for health and nutrition. I’m excited to introduce our 2’-Fucosyllactose (2’-FL) — a safe, consistent, and high-purity HMO produced via fermentation with Corynebacterium glutamicum.
Our R&D team, comprising former senior executives from Amyris and Evonik, brings world-class expertise to every step of the production process. Moreover, Xinfu’s record in Vitamin B5 manufacturing — commanding about 40% of global market share — demonstrates our ability to scale without compromising quality.
Whether you are looking to enhance infant nutrition products, functional foods, or dietary supplements, we are ready to support you with samples, technical insights, and a commitment to long-term collaboration.
Would you be open to a conversation? I’d love to hear more about your current projects and how we can assist.
Looking forward to staying in touch!
Best,
Qihan Wang
Regional Sales Manager
Hangzhou Xinfu Science & Technology Co., Ltd.
wangqihan@yifanyy.com
by "hmo.trade" <hmo.trade@xinfu-global.com> - 03:44 - 2 Jun 2025 -
HAPP BAR 25000 Puffs 2 flavors in 1 vape - EU warehouse 22 flavors with 3-7 work days fast delivery
Hi
Good day.
It's Amy from HAPP BAR Vapes, one of the top brands in China and sell more than 3 Millions each month. Have puffs range from 4000-10000puffs in eu warehouse with fast delivery.Highly recommend our Twin pod dual flavors disposable vape 2 in 1 - 25000puffs with Screen display below.
Sample trial order is welcomed. Also support custom logo and packaging.
Should you have any interest, please kindly let me know, so details can be sent accordingly.
Wait for your reply and further discussion.
You also can find me on whatsapp +86 137 6716 4681
Best regards
Amy Huang | Sales Manager
M:+86 137 6716 4681
www.happvape.com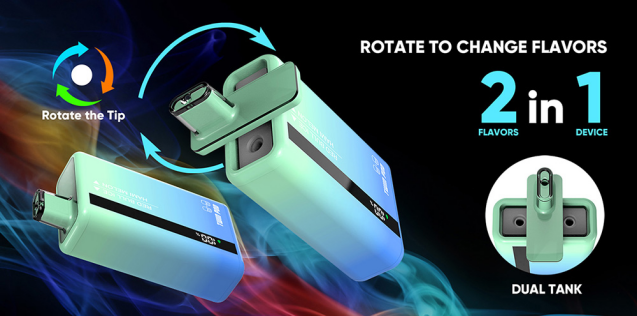
by "Puji Sennin" <pujisennin@gmail.com> - 02:47 - 2 Jun 2025